In the digital age, data is the new currency. Every organization, from small startups to global enterprises, relies on data to make decisions, improve services, and gain competitive advantages. However, as data becomes more valuable, it also becomes more vulnerable. Cyberattacks, data breaches, and privacy violations have made secure data sharing and computation a top priority. This is where Multi-Party Computation (MPC) comes into play.
Multi-Party Computation is a cryptographic technique that allows multiple parties to jointly compute a function over their inputs while keeping those inputs private. In simpler terms, MPC enables collaboration without compromising confidentiality. It ensures that no single participant learns anything beyond the final result of the computation.
As blockchain continues evolving into a foundational digital infrastructure, privacy-preserving technologies like MPC are becoming critical for enabling secure collaboration across decentralized systems. This aligns with the broader transformation explored in Blockchain as Public Infrastructure: The New Digital Railways.
This technology is revolutionizing industries such as finance, healthcare, supply chain, and artificial intelligence by enabling secure data collaboration. This article explores the fundamentals of MPC, its history, working principles, applications, benefits, challenges, and future potential.
What Is Multi-Party Computation?
Multi-party computation (MPC) is a cryptographic method that splits a private key into separate shares distributed across multiple independent parties. The concept can be summarized as “compute together, reveal nothing.”
For example, imagine several banks wanting to detect fraudulent transactions across their combined datasets. They cannot share customer data due to privacy laws, but they can use MPC to jointly analyze patterns and identify fraud without exposing any sensitive information.
MPC ensures that:
- Each participant’s input remains confidential.
- The computation is correct and verifiable.
- The final output is revealed only to authorized parties.
This makes MPC a cornerstone of privacy-preserving computation and a key enabler of secure data collaboration.
The Origins and Evolution of MPC
The concept of Multi-Party Computation dates back to the early 1980s. The first formal definition was introduced by Andrew Yao in 1982 through the concept of Yao’s Millionaires’ Problem. In this problem, two millionaires want to know who is richer without revealing their actual wealth. Yao’s solution laid the foundation for secure two-party computation.
Over the years, researchers extended Yao’s ideas to multiple parties, leading to the development of general-purpose MPC protocols. Early implementations were theoretical and computationally expensive, but advances in cryptography and computing power have made MPC practical for real-world use.
Key milestones in MPC development include:
- 1982: Yao’s Millionaires’ Problem introduced.
- 1986: Secure function evaluation (SFE) formalized.
- 1990s: Introduction of secret sharing and threshold cryptography.
- 2000s: Practical MPC protocols for small groups.
- 2010s: Industrial adoption in finance and data analytics.
- 2020s: Integration with blockchain, AI, and cloud computing.
Today, MPC is a mature technology with commercial applications across multiple sectors.
How Multi-Party Computation Works
At its core, MPC allows multiple parties to compute a function f(x₁, x₂, …, xₙ) where each party i holds a private input xᵢ. The goal is to compute the output y = f(x₁, x₂, …, xₙ) without revealing any xᵢ to others.
1. Secret Sharing
The most common approach to MPC is secret sharing. Each participant divides their input into multiple random “shares” and distributes them among all parties. No single share reveals any information about the original input, but when combined, they reconstruct the input.
For example, if Alice’s input is 10, she can split it into three shares: 4, 3, and 3. Each participant receives one share. Only by combining all three can the original value (10) be recovered.
2. Secure Computation
Once all inputs are shared, the parties perform computations on the shares rather than the actual data. This ensures that intermediate values remain hidden. The computation follows a predefined protocol that guarantees correctness and privacy.
3. Output Reconstruction
After the computation, the parties combine their output shares to reconstruct the final result. The output is revealed only to authorized participants, while the individual inputs remain secret.
Types of MPC Protocols
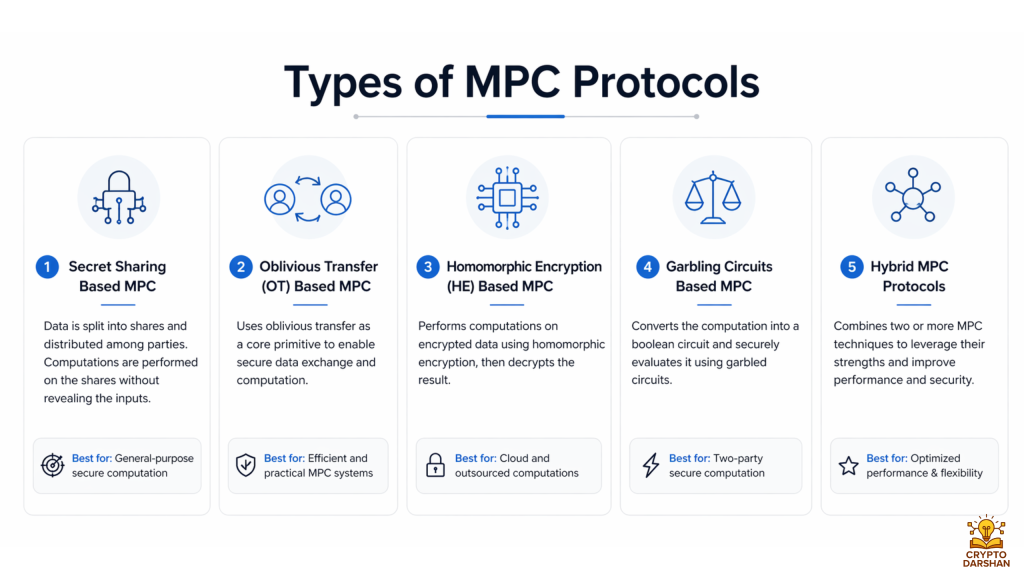
Different MPC protocols exist depending on the number of participants, trust assumptions, and performance requirements.
1. Yao’s Garbled Circuits
Used primarily for two-party computation, this protocol converts a function into a “garbled” circuit where each gate is encrypted. The parties evaluate the circuit without learning intermediate values.
2. Secret Sharing-Based Protocols
These protocols use additive or Shamir’s secret sharing to distribute data among participants. They are efficient for multi-party settings and support both arithmetic and Boolean operations.
3. Homomorphic Encryption-Based MPC
Homomorphic encryption allows computations to be performed directly on encrypted data. While computationally intensive, it provides strong security guarantees.
4. Threshold Cryptography
In threshold schemes, a secret (like a cryptographic key) is divided among multiple parties. Only a subset (threshold) of them can reconstruct the secret or perform operations.
5. Hybrid Protocols
Modern MPC systems often combine multiple techniques to balance performance, scalability, and security.
Key Properties of MPC
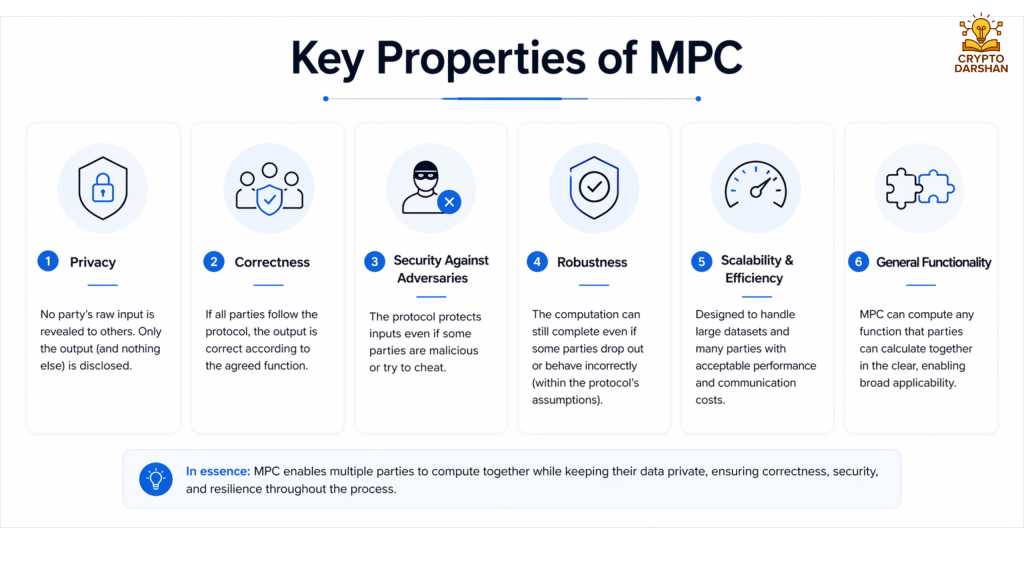
MPC protocols are designed to satisfy several essential properties:
- Privacy: No participant learns anything beyond the final output.
- Correctness: The output is guaranteed to be correct even if some parties act maliciously.
- Robustness: The protocol can tolerate a certain number of faulty or dishonest participants.
- Fairness: All parties receive the output simultaneously.
- Verifiability: Participants can verify that the computation was performed correctly.
These properties make MPC suitable for high-stakes applications where trust and confidentiality are critical.
Advantages of Multi-Party Computation
1. Enhanced Data Privacy
MPC allows organizations to collaborate on data analysis without exposing sensitive information. This is crucial for compliance with privacy regulations like GDPR and HIPAA.
2. Secure Collaboration
Multiple entities can jointly compute results without needing a trusted third party. This eliminates single points of failure and reduces the risk of data leaks.
3. Regulatory Compliance
By keeping data encrypted during computation, MPC helps organizations meet strict data protection standards.
4. Reduced Risk of Data Breaches
Since data is never exposed in plaintext, even if one party is compromised, the attacker gains no useful information.
5. Cross-Organizational Insights
MPC enables data-driven insights across organizations that would otherwise be impossible due to privacy constraints.
Challenges and Limitations

Despite its advantages, MPC faces several challenges:
1. Computational Overhead
MPC protocols are more resource-intensive than traditional computation. They require additional communication and processing power.
2. Network Latency
Since MPC involves multiple rounds of communication between parties, network delays can impact performance.
3. Complexity of Implementation
Designing and deploying MPC systems requires specialized cryptographic expertise.
4. Scalability
While modern protocols are improving, scaling MPC to hundreds or thousands of participants remains challenging.
5. Integration with Legacy Systems
Adopting MPC often requires re-engineering existing workflows and infrastructure.
Real-World Applications of MPC

1. Financial Services
Banks and financial institutions use MPC for secure risk analysis, fraud detection, and collaborative credit scoring. It allows them to share insights without exposing customer data.
2. Healthcare
Hospitals and research institutions use MPC to analyze patient data across organizations while maintaining confidentiality. This accelerates medical research and improves treatment outcomes.
3. Supply Chain Management
MPC enables companies to share supply chain data securely, improving transparency and efficiency without revealing proprietary information.
4. Digital Advertising
Advertisers and publishers use MPC to measure campaign performance without sharing user-level data, ensuring privacy compliance.
5. Machine Learning and AI
MPC supports privacy-preserving machine learning (PPML), allowing models to be trained on distributed datasets without exposing raw data.
6. Blockchain and Cryptocurrencies
MPC enhances blockchain security by enabling threshold signatures and decentralized key management. It prevents single points of failure in digital asset custody.
MPC in Blockchain and Web3

MPC plays a crucial role in the emerging Web3 ecosystem, where decentralization and privacy are key principles. It enables secure key management, private smart contracts, and confidential transactions.
1. Threshold Signatures
MPC allows private keys to be split among multiple nodes. No single node can sign a transaction alone, reducing the risk of key theft.
2. Private Smart Contracts
MPC enables smart contracts to process confidential data without revealing it on the blockchain.
3. Decentralized Identity
MPC supports privacy-preserving identity verification, allowing users to prove credentials without exposing personal data.
MPC vs. Other Privacy-Preserving Technologies
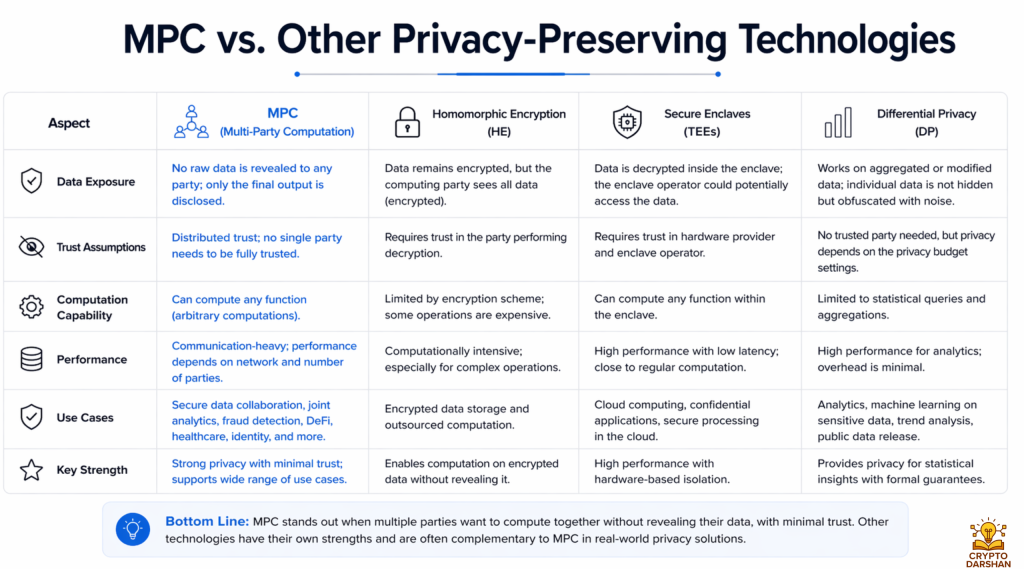
| Technology | Description | Strengths | Limitations |
| MPC | Joint computation without revealing inputs | Strong privacy, no trusted third party | High computational cost |
| Homomorphic Encryption | Computation on encrypted data | Mathematically strong security | Slow performance |
| Differential Privacy | Adds noise to data for anonymity | Scalable, simple | Reduced accuracy |
| Federated Learning | Model training on distributed data | Efficient for ML | Limited to specific use cases |
MPC often complements these technologies to create hybrid privacy-preserving systems.
Security Models in MPC

MPC protocols are designed under different adversarial models that define the level of trust and potential threats.
1. Semi-Honest Model
Participants follow the protocol but may try to learn extra information from received data. This model is easier to implement and efficient.
2. Malicious Model
Participants may deviate from the protocol to manipulate results or extract data. Protocols under this model are more secure but computationally heavier.
3. Covert Model
Participants may cheat only if they believe they won’t be caught. This model balances security and efficiency.
Security and trust are major concerns in automated trading ecosystems. These risks are particularly visible in copy trading platforms, where users rely on third-party strategies. As discussed in Copy Trading Crypto: Pros, Cons, and Hidden Risks Beginners Miss, privacy-preserving technologies like MPC can help strengthen security and reduce potential manipulation risks.
MPC in Cloud Computing
Cloud computing introduces new privacy challenges, as data is often processed by third-party servers. MPC mitigates these risks by enabling secure computation across cloud environments.
Benefits in Cloud Environments:
- Protects sensitive data from cloud providers.
- Enables multi-cloud collaboration.
- Supports secure analytics on encrypted datasets.
MPC can be integrated with confidential computing and secure enclaves for enhanced protection.
Performance Optimization in MPC
To make MPC practical, researchers and developers focus on improving efficiency through:
- Preprocessing: Performing heavy computations before the actual protocol starts.
- Parallelization: Running computations concurrently across multiple nodes.
- Optimized Communication: Reducing the number of communication rounds.
- Hardware Acceleration: Using GPUs or specialized chips for faster computation.
These optimizations make MPC suitable for real-time applications like financial trading and fraud detection.
Regulatory and Ethical Considerations

MPC aligns with global privacy regulations such as:
- GDPR (General Data Protection Regulation)
- CCPA (California Consumer Privacy Act)
- HIPAA (Health Insurance Portability and Accountability Act)
By ensuring data confidentiality, MPC helps organizations maintain compliance while enabling innovation. Ethically, it promotes responsible data sharing and prevents misuse of personal information.
The Future of Multi-Party Computation
The future of MPC is promising, with ongoing research and commercial adoption accelerating rapidly. Key trends include:
1. Integration with AI
MPC will power privacy-preserving AI models that can learn from distributed data sources without compromising privacy.
2. Decentralized Finance (DeFi)
MPC will enhance DeFi security by enabling multi-signature wallets and private transactions.
3. Interoperability
Future MPC systems will support seamless integration across different platforms and protocols.
4. Quantum-Resistant MPC
As quantum computing advances, researchers are developing MPC protocols resistant to quantum attacks.
5. Standardization
Industry-wide standards will emerge to ensure interoperability, security, and compliance.
Case Studies

Case Study 1: Secure Credit Scoring
Several banks collaborated using MPC to compute credit scores based on shared data. The system improved accuracy by 25% while maintaining full compliance with privacy laws.
Case Study 2: Medical Research Collaboration
Hospitals across Europe used MPC to analyze genomic data for cancer research. The project enabled large-scale analysis without exposing patient data.
Case Study 3: Fraud Detection in Payments
Payment processors used MPC to detect cross-platform fraud patterns. The system reduced false positives and improved detection rates.
Emerging Trends and Innovations in MPC
The next generation of MPC is being shaped by several technological and societal trends that are expanding its reach and capabilities.
1. MPC-as-a-Service (MPCaaS)
Cloud providers and cybersecurity firms are beginning to offer MPC as a managed service. This model allows organizations to access secure computation capabilities without building complex infrastructure. MPCaaS platforms handle protocol management, scalability, and compliance, making adoption easier for enterprises.
2. Integration with Zero-Knowledge Proofs
Combining MPC with zero-knowledge proofs (ZKPs) enhances both privacy and verifiability. ZKPs allow one party to prove that a computation was done correctly without revealing the underlying data. This hybrid approach is gaining traction in blockchain and financial auditing.
3. Edge Computing and IoT
As billions of IoT devices generate sensitive data, MPC can enable secure analytics at the edge. Devices can jointly compute insights without sending raw data to centralized servers, reducing latency and improving privacy.
4. Secure Voting Systems
MPC is being explored for digital voting systems to ensure transparency and voter privacy. It allows votes to be tallied securely without revealing individual choices, strengthening trust in electronic elections.
5. Cross-Border Data Collaboration
Global organizations face challenges in sharing data across jurisdictions due to varying privacy laws. MPC provides a legal and technical framework for cross-border collaboration by ensuring that data never leaves its origin in plaintext form.
6. Privacy-Preserving Genomics
In genomics research, MPC enables scientists to analyze genetic data from multiple institutions without exposing individual genomes. This accelerates discoveries in personalized medicine while maintaining ethical standards.
7. Integration with Secure Hardware
Combining MPC with Trusted Execution Environments (TEEs) like Intel SGX or ARM TrustZone enhances performance and security. TEEs handle sensitive computations locally, while MPC ensures distributed trust.
Economic and Business Impact of MPC
MPC is not just a technical innovation—it’s a business enabler. By unlocking secure collaboration, it creates new economic opportunities.
1. Data Monetization Without Exposure
Organizations can monetize insights derived from private data without selling or sharing the data itself. This creates new revenue streams while maintaining compliance.
2. Competitive Collaboration
MPC allows competitors to collaborate on shared challenges, such as fraud detection or sustainability, without revealing trade secrets.
3. Reduced Compliance Costs
By embedding privacy into computation, MPC reduces the need for costly data anonymization and legal reviews.
4. Trust as a Business Asset
Companies that adopt MPC demonstrate a commitment to privacy and security, strengthening customer trust and brand reputation.
Implementing MPC in Organizations

Steps to Adoption:
- Identify Use Cases: Determine where data collaboration is limited by privacy concerns.
- Select Protocols: Choose MPC protocols suited to the organization’s needs.
- Build Infrastructure: Deploy secure communication channels and computation nodes.
- Integrate with Existing Systems: Ensure compatibility with current data pipelines.
- Test and Validate: Conduct pilot projects to measure performance and security.
- Scale and Optimize: Expand deployment across departments or partners.
Best Practices:
- Use hybrid approaches combining MPC with other privacy technologies.
- Regularly audit protocols for vulnerabilities.
- Educate stakeholders about MPC’s benefits and limitations.
- Partner with academic and industry experts for continuous improvement.
Frequently Asked Questions(FAQ)

1. What is Multi-Party Computation (MPC)?
Multi-Party Computation (MPC) is a cryptographic technique that allows multiple parties to compute a result together without revealing their private data to each other. Each participant keeps their input secret while the system jointly produces the final output.
2. Why is MPC important for data security?
MPC protects sensitive information during collaboration. Organizations can analyze shared data without exposing confidential details such as financial records, personal data, or proprietary algorithms.
3. How does Multi-Party Computation work?
MPC divides data into encrypted fragments called secret shares. These shares are distributed among participants. Each party performs calculations on their share, and the combined result produces the final computation without revealing the original data.
4. What are the key advantages of MPC?
Major benefits include:
- Strong privacy protection
- Secure data collaboration
- Reduced risk of data breaches
- Compliance with data privacy regulations
- Trustless cooperation between organizations
5. What industries are using MPC today?
MPC is gaining adoption in several industries:
- Finance – secure trading and risk analysis
- Healthcare – privacy-preserving medical research
- Cybersecurity – secure authentication systems
- Blockchain and crypto – wallet key management
- Advertising and data analytics
6. How is MPC used in blockchain and cryptocurrency?
In blockchain systems, MPC is used to secure private keys. Instead of storing a single private key in one location, the key is split across multiple parties, preventing a single point of failure and improving wallet security.
7. What is the difference between MPC and encryption?
Encryption protects data at rest or in transit, while MPC allows secure computation on encrypted data without revealing the underlying information.
8. What are the challenges of Multi-Party Computation?
Some challenges include:
- High computational complexity
- Increased communication between participants
- Slower performance compared to traditional computation
- Complex implementation
However, modern cryptographic research is improving efficiency.
Conclusion
Multi-Party Computation represents a paradigm shift in how organizations handle data privacy and collaboration. By enabling secure computation without revealing private inputs, MPC bridges the gap between data utility and confidentiality. It empowers industries to unlock new insights, foster innovation, and maintain trust in an increasingly data-driven world.
As technology evolves, MPC will become a foundational component of secure digital ecosystems, powering everything from financial systems to AI models and decentralized networks. Its ability to protect privacy while enabling collaboration makes it one of the most transformative technologies of the 21st century.